Phishing an Ever-Present Cyber Threat
Phishing is digital theft. Cybercriminals make money when employees, in a hurry or under duress, open and respond to emails, messages, phone calls, or social media posts. Any type of communication can host phishing content. Phishing messages are intended to convince users to open them and either provide sensitive information or provide an opening to the network to plant ransomware or malware.
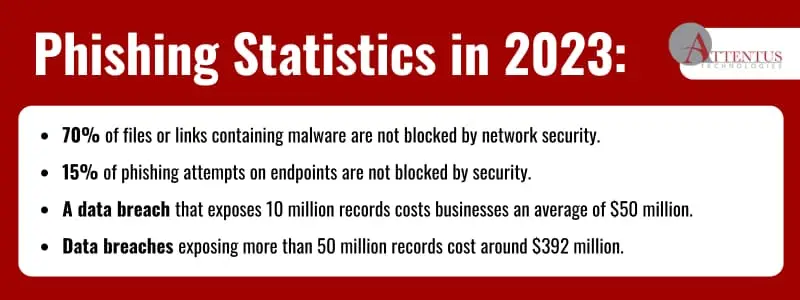
Your business will get attacked through phishing. It’s only a matter of finding a single employee to let them in. The objective is to prevent phishing attempts from reaching employees and manage and survive attacks. Consider this statistic: 84% of employees respond to a phishing scam by replying with sensitive information or clicking a link on a business network.
This guide defines phishing, explains its role in compromising business networks to steal business data, and provides security strategy tips to prevent and manage cyberattacks.
What is phishing, and why is it important?
Phishing represents the earliest form of social engineering in the digital age, where a cybercriminal sends an authentic-looking message via email, SMS, or social media post. Within a business network, phishing is a method cybercriminals employ to infiltrate and compromise systems, either by stealing data or holding it hostage for a ransom.
Most phishing communications lure victims into clicking a link that loads malware to a system. Typically, these attempts create a sense of urgency or threat to motivate users to click before they think. It takes only one employee falling for a phishing scam to initiate a cyberattack.
Phishing criminals exploit those who are busy, stressed, distressed, or otherwise vulnerable. Phishing attacks focus on vulnerabilities and have become the number one method for planting ransomware into a system.
If your business lacks effective security endpoints like APIs and databases, you’re at high risk. Prepare now, as it’s not a matter of whether your business will be attacked but whether it can manage the attack and survive.
Common types of phishing attacks targeting business data
Phishing and cyberattacks impact businesses of all sizes. Despite ongoing security training for employees, some still fall victim to simple or complex phishing scams. Many employees often react quickly when emails or messages come from managers, upper management, or coworkers. Employees frequently respond before thinking it through.
Think of anything that may cause a person to panic or become quickly distressed, and you have the latest phishing scam. Most people have heard of phishing scams where communications are from well-known financial institutions and government offices like the IRS or Immigration. Without constant oversight and thorough consideration of every single communication an employee receives, it’s understandable how phishing continues to claim victims. Here are a few of the more common methods that bad actors use:
- Pretexting: Using already stolen pieces of personal data to convince a person it’s legitimate.
- Spear phishing: Subject matter pertains to the business, like a human resources request or an instruction coming from the president, CEO, or other leadership.
- Rogue: Fake antivirus software unknowingly chosen by employees or businesses for cybersecurity protection.
- Water-holing: Cybercriminals gain access to a website used by the business or employees and then gain access to authentication credentials.
Why use phishing?
Why not? Cybercriminals run organized businesses that steal and then sell data. Phishing has been around for decades and is still profitable. Phishing avoids the dangers of hacking into a system directly by obtaining information directly.
Fine, phishing can impact a business, but why don’t security systems keep it out? Effective cybersecurity does prevent security incidents. However, it’s critical for an I.T. system to be assessed by security professionals to look for endpoints, APIs, or business partner systems that are ineffectively secured or whose security is not up to date.
Securing a business is a complex endeavor across all industries. Identifying vulnerabilities within the complete spectrum of I.T. infrastructure, devices, and business systems is an ongoing and dynamic challenge. The landscape of security threats evolves daily, becoming more sophisticated. Maintaining a business network that is consistently up-to-date and compliant with the latest security patches and updates demands substantial resources. However, this investment in vigilance and adaptation is essential for the continual improvement of the security posture, ensuring resilience in the face of ever-evolving cyber threats.
Tips for recognizing and preventing phishing attacks
Securing your business against cyber threats demands a comprehensive approach that goes beyond conventional measures. Consider the following essential cybersecurity practices to fortify your defenses and safeguard your valuable assets:
- Continuous, proactive server maintenance and security management.
- Continuous system monitoring to detect phishing or other threats.
- Understand the complexity of your cloud platforms, providers, apps, third-party business partners, APIs, and data connections.
- Proper implementation of MFA (multi-factor authentication) for all network access points and business applications.
- Train employees on security and keep it as a top priority.
- Implement strong network border security.
- Utilize protocols designed to filter email communications.
- Secure all endpoints and enable continuous security to block malicious activity.
The steps above are only a small sampling of business security measures. In addition, the business needs a plan for addressing and managing security incidents should they occur. A security management team is essential for making decisions quickly while addressing legal concerns and contacting authorities. Does it sound like a lot of complex work? It is. Doing it badly can cost you financially or make your business fail.
Looking to fortify your cybersecurity defenses? Attentus is dedicated to optimizing your business’s security measures and ensuring peak performance while providing cutting-edge protocols that safeguard and enhance your operations. Our commitment to exceptional security assessment and management ensures your business stays secure and operational. As your trusted partner, we tailor our services to your unique needs, actively supporting your growth and success now and into the future. Partner with Attentus, Seattle’s foremost provider of I.T. services, and make your security strategy exceptionally effective without the fear factor.
Consider getting an accurate price quote in 30 minutes.